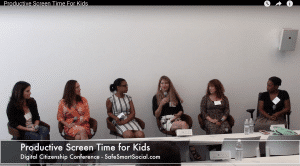
On November 11, 2016 I was invited to participate in a panel discussion and present in a breakout session at the Safe Smart Social Conference at the Microsoft Corporate Headquarters in Los Angeles, CA. Here is a link to the panel presentation with thought leaders in child screen safety. My favorite takeaway?
***
How can we collaborate with technology to build a connection with our kids?
Strive to have a strong, fun, connection with your children that includes an ongoing dialogue; one of the best ways to achieve that connection is with tech. If children see us as a partner in tech, then we can keep the conversation open. Remember that the partnership between tech and your connection with your child is the most important. –Dr. Tracy Bennett, GetKidsInternetSafe