It’s every teen’s dream to have unmonitored texting through WiFi, without having to ask parent permission or use expensive data. With instant messaging apps like Kik, all you need is an Internet-connected screen device and, voila, there’s your private Internet portal. Kik is most commonly used among middle schoolers, which translates to online teen hijinks, some innocent and some not-so-innocent. Apps like these are why screen safety agreements among parents and their teens are so vital. My Screen Safety Toolkit is a great instrument for navigating how to monitor your child without hurting your relationship.
What is Kik?
Kik is a free mobile application that is used for instant messaging (IM). It is most commonly used on handheld screen media that connect to WiFi (like smartphones, iPods, and tablets). A Kik account allows the user to send and receive messages with other Kik users. It’s similar to texting, but instead of using “minutes” or a data plan, it sends messages through WiFi. Kik’s Terms of Service state that users must be 13 years or older.
What are Kik’s popular features?
- Kik looks and acts like a basic SMS text messaging function.
- You can invite friends or family to use Kik through text, social media, or email.
- Just like regular text messaging, you will receive notifications when your messages were sent and delivered. Not only can you tell when someone has received your message, but you can also see when they have read it and are typing back.
- You can send pictures, videos, and texts to peers or even strangers.
- The main page when you open the app is a list of your Kik conversations.
What are the privacy options?
- Kik has limited privacy settings.
- I recommend that you only tell people you know your personal username. To keep it private, do NOT post it on any other social media sites where strangers may see it.
- You have the ability to block users (searched by username or name) if you are being cyberbullied. Simply go to “Chat Settings,” then select “Block List.”

 How long has it been around and how popular is it?
How long has it been around and how popular is it?
- Kik became available to the public in October 2010. In just two weeks it had about one million users.
- Popular among teenagers, most young adults don’t use this application, due to the fact that most of them already use texting that’s provided with data plans.
What are the risks for use?
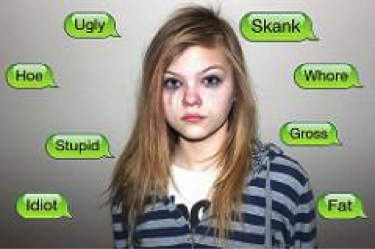
Cyberbully potential:
- Due to the fact that Kik messages do not show up on wireless plans like text messaging, it makes it easier for the kids to send hurtful messages.
- Cyberbullying commonly occurs with Kik.
-
- If an enemy from school gets your username they may message you on Kik and send you insults or threats. For example, there are many reports about Kik users receiving messages telling them they should just die because no one cares about them.
- Rebecca Sedwick was a twelve year-old girl who was bullied on Kik. Her mother was unaware of the Kik app even though she would sometimes go through her phone. Rebecca had posted photos of herself cutting her arms. Peers responded asking her why she was even alive, calling her names. Before committing suicide she changed her Kik name to, “That Dead Girl.”
Making poor decisions:
- It’s possible to have conversations with strangers on Kik, making connection with an online predator dangerously easy.
- Sexting is a risk with this Kik.
Inappropriate content potential:
- Due to sexting, Kik users may receive graphic photos from peers or strangers.
- Drug deals and sex hookups are common on Kik.
- Parental monitoring is difficult because chats can easily be deleted.
Due to the potential for unmonitorable interaction with peers and strangers and difficulty with monitoring, GetKidsInternetSafe classifies Kik as a red light app. The anonymity and easy delete potential can lead to dangerous conversations. To learn more about the social media applications your child may be using, check out a The GetKidsInternetSafe Sensible Parent’s Guide to Tumblr.

I’m the mom psychologist who will help you GetKidsInternetSafe.
Onward to More Awesome Parenting,
Tracy S. Bennett, Ph.D.
Mom, Clinical Psychologist, CSUCI Adjunct Faculty
GetKidsInternetSafe.com
Photo Credit:
Informal Gluttony by Kat Northern Lights Man, CC BY-NC 2.0
Cyberbullying, would you do it? by kid-josh, CC BY-NC-SA 2.0
Pro Juventute Aufklärungskampagne ‚Sexting’ Themenbild_04, CC BY 2.0